How Session Hijacking Attacks Bypass MFA in U.S. Businesses
Most businesses believe enabling MFA (Multi-Factor Authentication) is enough to stop attackers.
Unfortunately… it’s not.
A growing number of attacks are now bypassing MFA entirely using session hijacking techniques—and many U.S. businesses don’t even realize it’s happening.
⚠️ What Is Session Hijacking (In Simple Terms)?
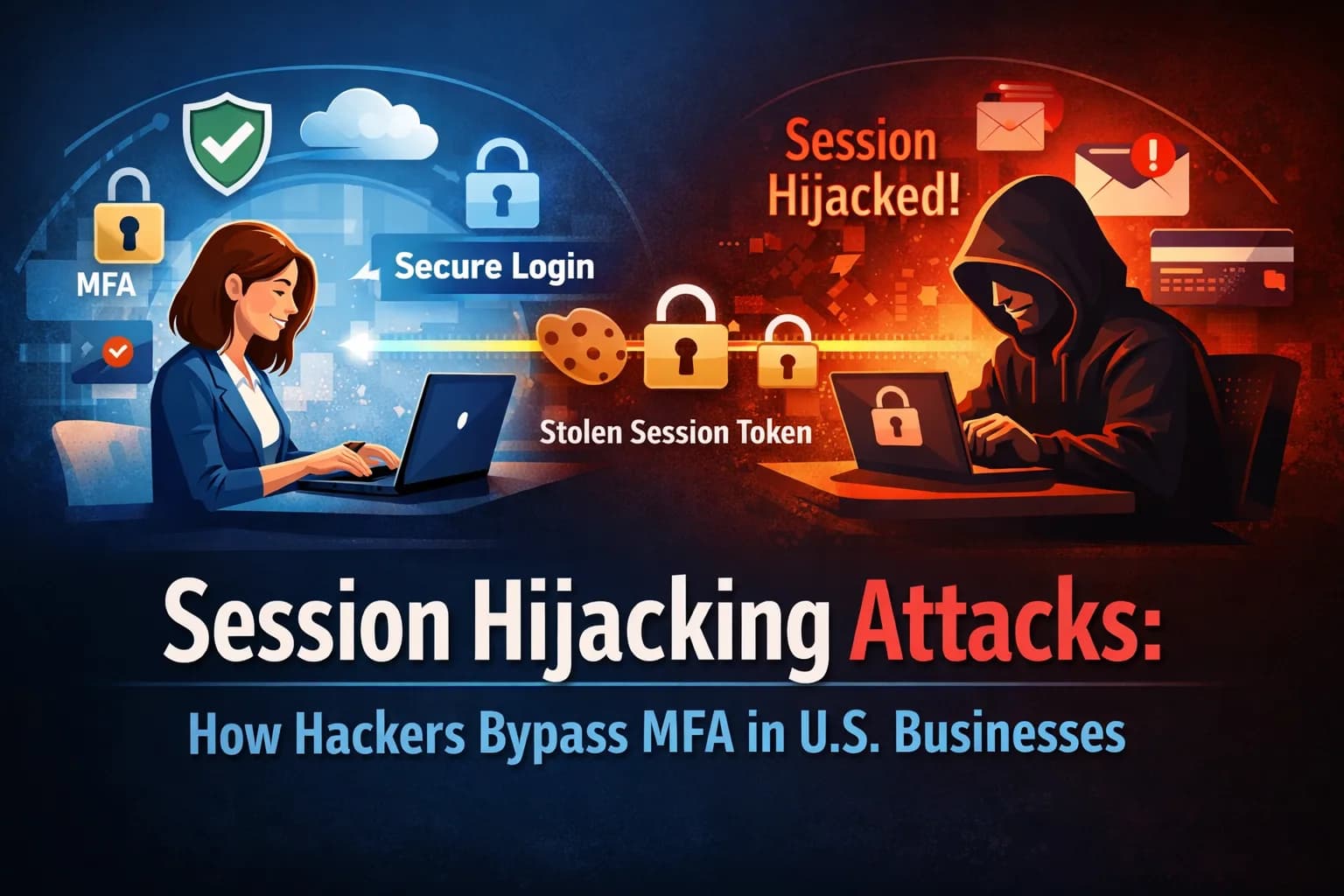
When you log in to a website, your system creates a session token to keep you authenticated.
Instead of stealing your password, attackers steal this session token.
👉 Result: They gain access without needing MFA again
🚨 How Attackers Bypass MFA
Here’s how it typically works:
1. User logs in (enters password + MFA ✅)
2. A session is created and stored in the browser
3. Malware or phishing steals the session token
4. Attacker reuses the session → instant access
•No password.
•No MFA prompt.
•Just access.
🔍 Why This Is Dangerous for Businesses
Session hijacking is especially risky because:
* It completely bypasses MFA protection
* It’s hard to detect without monitoring
* Attackers can access emails, files, and dashboards silently
For freelancers and small businesses, this can lead to:
* Client data exposure
* Account takeovers
* Financial and reputational damage
🛡️ How to Reduce the Risk
While you can’t eliminate the risk completely, you can reduce it:
* Use secure browsers or browser isolation
* Enable device and session monitoring
* Avoid clicking unknown links (phishing is a major entry point)
* Use endpoint security tools
💡 Key Takeaway
MFA is important—but it’s not bulletproof.
Session hijacking shows that modern attacks focus on sessions, not just credentials.
🚨 Want the Full Breakdown + Real Fixes?
I’ve explained the attack methods, real-world risks, and advanced protection strategies in detail here:
👉 Read the full blog:
How Session Hijacking Attacks Bypass MFA in U.S. Businesses
💬 Let’s Discuss
Do you think MFA is still enough for security today?